NCSS Threat Feeds Portal
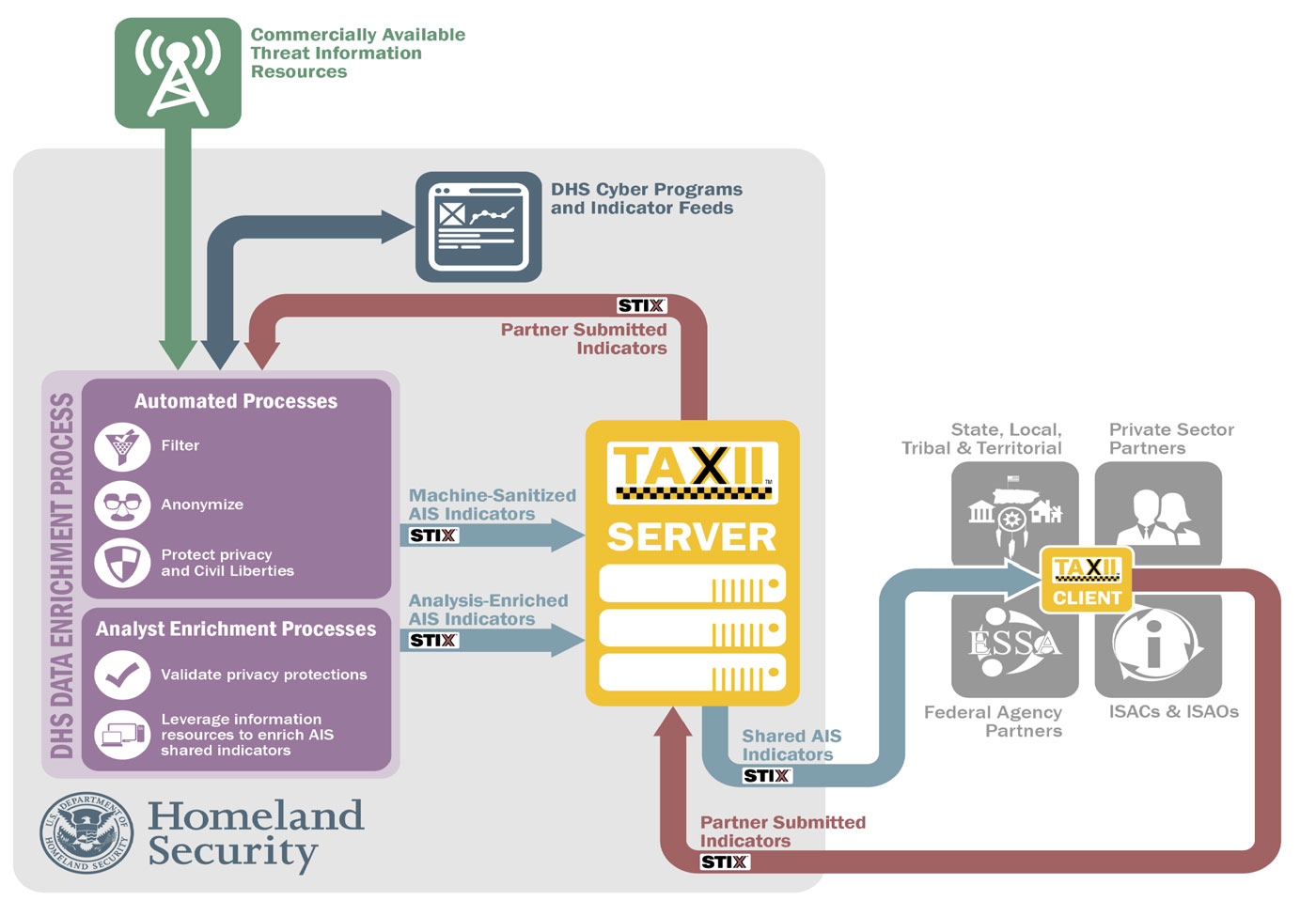
The NCSS, as an Information Sharing and Analysis Organization, (ISAO), participates in the Automated Indicator Sharing (AIS) Program run by the Department of Homeland Security (DHS).
Our IT infrastructure is compliant with the AIS program and receives weekly Indicators of Compromise (IOC) through polling the DHS AIS server and receiving their latest threat feeds.
These threat feeds, better known as “Indicators of Compromise” (IOC) are defined as information that describes or identifies:

Malicious reconnaissance, including anomalous patters of communications that appear to be transmitted for the purpose of gathering technical information related to a cybersecurity threat or security vulnerability;

A method of defeating a security control or exploitation of a security vulnerability;

A security vulnerability, including anomalous activity that appears to indicate the existence of a security vulnerability;

A method of causing a user with legitimate access to an information system or information that is stored on, processed by, or transiting an information system to unwittingly enable the defeat of a security control or exploitation of a security vulnerability;

Malicious cyber command and control

The actual or potential harm caused by an incident, including a description of the information exfiltrated as a result of a particular cybersecurity threat;

Any other attribute of a cybersecurity threat, if disclosure of such attribute is not otherwise prohibited by law; or

Any combination of the above.
These indicators can be used to block or prevent malicious actors from stealing your data, damaging systems and IT infrastructure or holding your systems hostage via ransomware. Downloading and screening these indicators for your use, or leveraging a Threat Intelligence platform will provide your organization an added security protection.
How it Works:
NCSS participates with the DHS National Cybersecurity and Communications Integration Center (NCCIC), in the AIS program, which allows bidirectional sharing of cyber threat indicators. The NCSS has built the technical capability to exchange indicators machine-to-machine with DHS. The NCSS polls the DHS server weekly and downloads the IOCs, and NCSS members can receive these indicators and use them in their own network defense efforts.
NCSS members who share indicators through our incident reporting portal, will not be identified as the source of the indicators. Sharing incident data via the NCSS portal, provides your company data breach protection from litigation and liability actions as defined by the Cybersecurity Information Sharing Act of 2015.
NCSS members who opt in for this free service will have to build their own technical capability to receive the IOCs. Additionally, you will have to validate and vet the indicators you receive from the feed, because DHS’s doesn’t pre-screen these indicators. Their goal is to share the data as quickly as possible, so speed is the driver. As an example, included in the broadcast are indicators for the oil and gas industry, that might not have applicability to your specific industry. So using a filter, your team can filter out the non-applicable indicators. Once screened, your team could load the IOCs to your firewall in order to block malicious activity.

Another approach your company could consider is to use a Threat Intelligence Platform to receive and vet the indicators. Several products on the market include:
If your company is interested in receiving this free threat feed from the NCSS Threat Feed Portal, become a member:
If you are already a member, contact us through our Ask an Expert:










